Getting Started with Trezor: Your Ultimate Guide to Secure Crypto
Step-by-step guidance for beginners and mid-level crypto users to set up and maximize Trezor hardware wallets via Trezor.io/start.
Why a Hardware Wallet Matters
For anyone diving into cryptocurrency, security is everything. Digital coins are highly attractive targets for hackers, phishing scams, and malware. While software wallets and exchange wallets are convenient, they are often vulnerable to online attacks.
Hardware wallets, like Trezor, provide offline storage for your private keys, meaning your crypto never touches an internet-connected device. Think of it as a vault: your coins are inside a safe, and you hold the key.
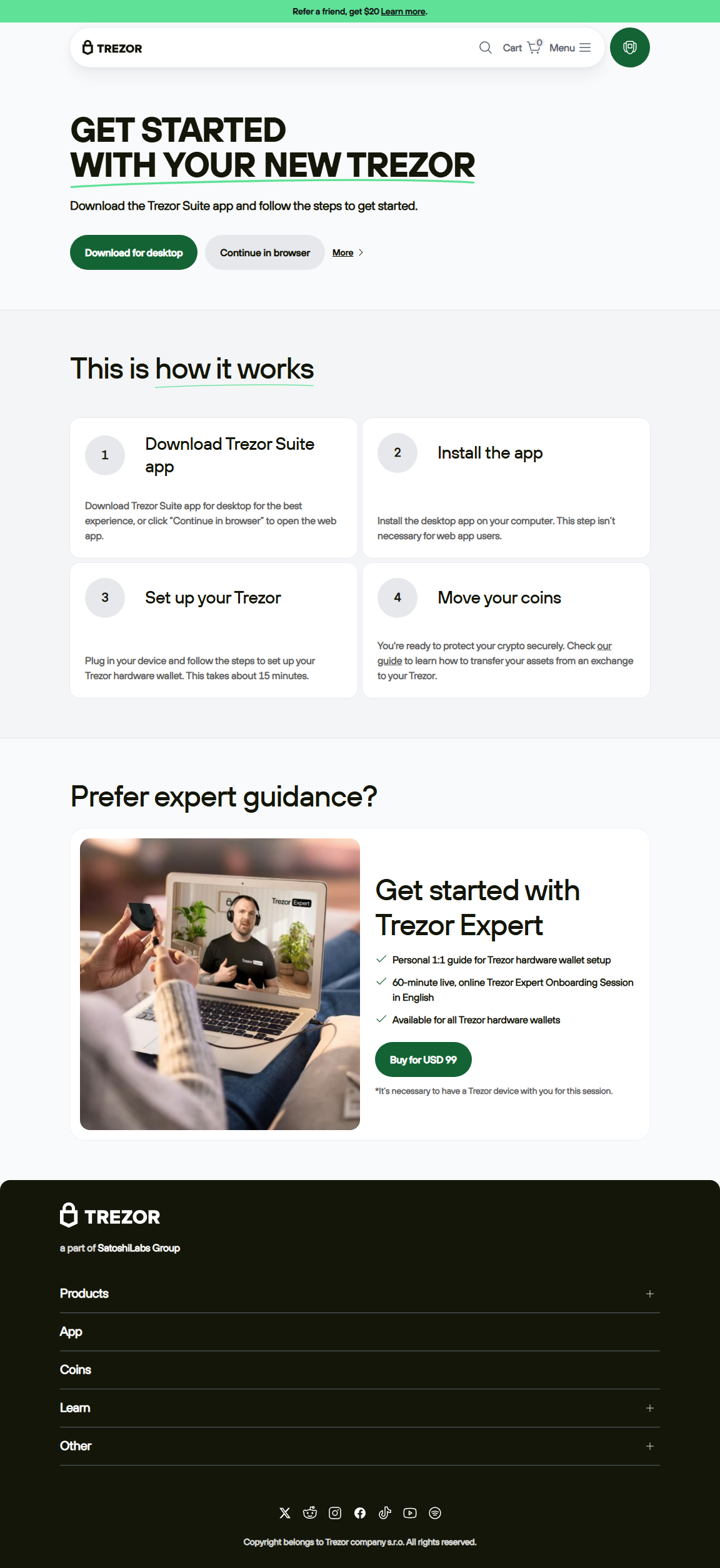
Step-by-Step: Getting Started with Trezor.io/start
Step 1: Visit the Official Start Page
Navigate to Trezor.io/start. This page is your gateway to setting up your Trezor wallet safely. Here you’ll download the Trezor Bridge software that allows your device to communicate with your computer.
Step 2: Connect Your Trezor Device
Plug in your Trezor using the supplied USB cable. Your computer should recognize the device, and the Trezor Bridge will handle the connection. The device will display a welcome screen with instructions.
Step 3: Initialize Your Wallet
Follow the on-screen instructions to either:
- Create a new wallet.
- Recover an existing wallet using your 12–24 word recovery seed.
Write down your recovery seed carefully. This is the only backup if your device is lost or damaged.
Step 4: Set a PIN Code
The Trezor will prompt you to set a PIN. This adds an extra layer of protection, so even if someone gets hold of your device, they cannot access your funds without the PIN.
Trezor vs. Other Wallets: Quick Comparison
| Feature | Trezor | Software Wallet | Exchange Wallet |
|---|---|---|---|
| Security | High (offline) | Medium (online) | Low (hack-prone) |
| Ease of Use | Medium | High | High |
| Cost | $60-$200 | Free | Free |
| Best For | Long-term security & holdings | Daily transactions | Trading on exchanges |
Frequently Asked Questions (FAQs)
A: Yes! Use your 12–24 word recovery seed to restore access on a new Trezor device or compatible wallet.
A: Absolutely. Trezor supports thousands of cryptocurrencies, including Bitcoin, Ethereum, Litecoin, and many ERC-20 tokens.
A: Yes. With the Trezor Suite mobile app or compatible third-party wallets, you can manage crypto on the go.
Advanced Tips for Mid-Level Users
- Multi-signature wallets: Increase security by requiring multiple approvals for transactions.
- Passphrase protection: Add an extra layer beyond your recovery seed to prevent unauthorized access.
- Firmware updates: Regularly update your Trezor to benefit from the latest security improvements.
- Cold storage strategy: Store the bulk of your crypto offline and only keep a small amount for trading.
Conclusion: Why Trezor.io/start is Your First Step to Crypto Security
Starting your journey with Trezor.io/start ensures that your cryptocurrency remains secure from online threats. Hardware wallets combine offline protection with ease of use, making them essential for both beginners and mid-level users aiming for long-term safety.
By following the setup steps, understanding best practices, and applying advanced tips, you can confidently store, manage, and grow your crypto portfolio. Remember: in the crypto world, control over your private keys equals control over your wealth.